- Ssh-keygen Aes-128-cbc
- Aes 128 Cbc Key Size
- Crypto.createcipheriv('aes-128-cbc' Key Iv)
- Aes 128 Cbc Sha
What is AES CBC
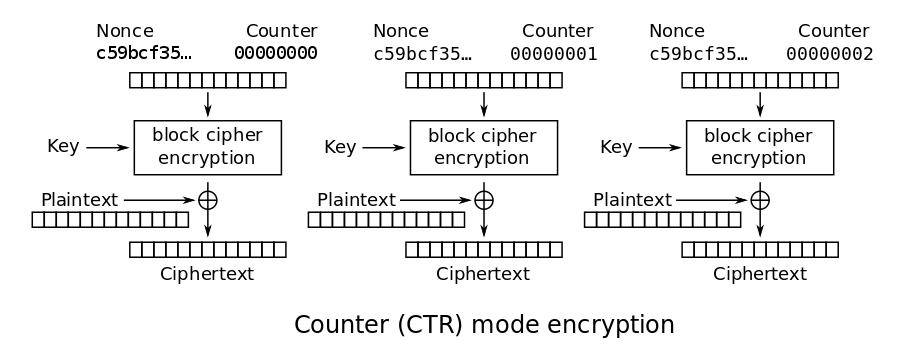
AES-CBC (cipher block chaining) mode is one of the most used symmetric encryption algorithms. The data size must be nonzero and multiple of 16 bytes, which is the size of a “block”. The data is split into 16-byte blocks before encryption or decryption is started, then the operation is performed on each of the blocks. Each block is connected (“chained”) to the two blocks before and after it, respectively. i.e., a block takes a 16-byte IV (initialization vector) from its immediately previous block as input, and outputs a 16-byte IV to the block immediately following it. Of course, the 16-byte ciphertext is also output. The very first block of data (where its previous block does not exist) takes the IV as input from the user; the last block outputs the IV to the user.
- Give our aes128 encrypt/decrypt tool a try! Aes128 encrypt or aes128 decrypt any string with just one mouse click.
- AES-128 uses ten rounds, AES-192 uses twelve rounds, and AES-256 uses fourteen rounds. Each added round reduces the chance of a shortcut attack of the kind that was used to attack AES-128 back 2011. As already noted as a consequence of this attack an additional four rounds were added to AES-128 in order to improve its safety margins.
You can use Media Services to deliver HTTP Live Streaming (HLS) and Smooth Streaming encrypted with the AES by using 128-bit encryption keys. Media Services also provides the key delivery service that delivers encryption keys to authorized users.
Very important note: choice of IV is critical to the security of CBC mode. The requirement is that the initial IV must be “unpredictable”, in other words, randomly generated before the encryption starts. Never use a hardcoded IV! Never pick the IV from a well-known database! Once encryption is completed, the value of IV is not a secret, and can be transmitted to the decryptor in plaintext.
Ssh-keygen Aes-128-cbc
 -->
-->Applies to
- Windows 10
Aes 128 Cbc Key Size

With Windows Autopilot, you can configure BitLocker encryption settings to get applied before automatic encryption starts. This configuration makes sure the default encryption algorithm isn't applied automatically. Other BitLocker policies can also be applied before automatic BitLocker encryption begins.
The BitLocker encryption algorithm is used when BitLocker is first enabled. The algorithm sets the strength for full volume encryption. Available encryption algorithms are: AES-CBC 128-bit, AES-CBC 256-bit, XTS-AES 128-bit, or XTS-AES 256-bit encryption. The default value is XTS-AES 128-bit encryption. See BitLocker CSP for information about the recommended encryption algorithms to use.
To make sure the BitLocker encryption algorithm you want is set before automatic encryption occurs for Autopilot devices:
- Configure the encryption method settings in the Windows 10 Endpoint Protection profile to the encryption algorithm you want.
- Assign the policy to your Autopilot device group. The encryption policy must be assigned to devices in the group, not users.
- Enable the Autopilot Enrollment Status Page (ESP) for these devices. If the ESP isn't enabled, the policy won't apply before encryption starts.
An example of Microsoft Intune Windows Encryption settings is shown below.
A device that is encrypted automatically will need to be decrypted before changing the encryption algorithm.
The settings are available under Device Configuration > Profiles > Create profile > Platform = Windows 10 and later, Profile type = Endpoint protection > Configure > Windows Encryption > BitLocker base settings, Configure encryption methods = Enable.
It's also recommended to set Windows Encryption > Windows Settings > Encrypt = Require.
Requirements
Crypto.createcipheriv('aes-128-cbc' Key Iv)
Windows 10, version 1809 or later.